2 Introduction to Transparent Data Encryption
Transparent Data Encryption enables you to encrypt sensitive data, such as credit card numbers or Social Security numbers.
- What Is Transparent Data Encryption?
Transparent Data Encryption (TDE) enables you to encrypt sensitive data that you store in tables and tablespaces. - Benefits of Using Transparent Data Encryption
Transparent Data Encryption (TDE) ensures that sensitive data is encrypted, meets compliance requirements, and provides functionality that streamlines encryption operations. - Who Can Configure Transparent Data Encryption?
To configure Transparent Data Encryption (TDE), you must be granted either theSYSKMadministrative privilege or theADMINISTER KEY MANAGEMENTsystem privilege. - Types and Components of Transparent Data Encryption
Transparent Data Encryption can be applied to individual columns or entire tablespaces. - Transparent Data Encryption in a Multitenant Environment
In a multitenant environment, you can configure keystores for either the entire container database (CDB) or for individual pluggable databases (PDBs). - How Configuring Transparent Data Encryption Works
To configure Transparent Data Encryption, you must perform a one-time setup before you create keystores and encrypt data. - Transparent Data Encryption Keystore Search Order
The search order for the TDE keystore depends on how you have set either the instance initialization parameters, thesqlnet.oraparameters, or the environment variables.
Parent topic: Using Transparent Data Encryption
What Is Transparent Data Encryption?
Transparent Data Encryption (TDE) enables you to encrypt sensitive data that you store in tables and tablespaces.
After the data is encrypted, this data is transparently decrypted for authorized users or applications when they access this data. TDE helps protect data stored on media (also called data at rest) in the event that the storage media or data file is stolen.
Oracle Database uses authentication, authorization, and auditing mechanisms to secure data in the database, but not in the operating system data files where data is stored. To protect these data files, Oracle Database provides Transparent Data Encryption (TDE). TDE encrypts sensitive data stored in data files. To prevent unauthorized decryption, TDE stores the encryption keys in a security module external to the database, called a keystore.
You can configure Oracle Key Vault as part of the TDE implementation. This enables you to centrally manage TDE keystores (called TDE wallets in Oracle Key Vault) in your enterprise. For example, you can upload a software keystore to Oracle Key Vault and then make the contents of this keystore available to other TDE-enabled databases.
Related Topics
Parent topic: Introduction to Transparent Data Encryption
Benefits of Using Transparent Data Encryption
Transparent Data Encryption (TDE) ensures that sensitive data is encrypted, meets compliance requirements, and provides functionality that streamlines encryption operations.
Benefits are as follows:
-
As a security administrator, you can be sure that sensitive data is encrypted and therefore safe in the event that the storage media or data file is stolen.
-
Using TDE helps you address security-related regulatory compliance issues.
-
You do not need to create auxiliary tables, triggers, or views to decrypt data for the authorized user or application. Data from tables is transparently decrypted for the database user and application. An application that processes sensitive data can use TDE to provide strong data encryption with little or no change to the application.
-
Data is transparently decrypted for database users and applications that access this data. Database users and applications do not need to be aware that the data they are accessing is stored in encrypted form.
-
You can encrypt data with zero downtime on production systems by using online table redefinition or you can encrypt it offline during maintenance periods.
-
You do not need to modify your applications to handle the encrypted data. The database manages the data encryption and decryption.
-
Oracle Database automates TDE master encryption key and keystore management operations. The user or application does not need to manage TDE master encryption keys.
Parent topic: Introduction to Transparent Data Encryption
Who Can Configure Transparent Data Encryption?
To configure Transparent Data Encryption (TDE), you must be granted either the SYSKM administrative privilege or the ADMINISTER KEY MANAGEMENT system privilege.
A user can authenticate as a security administrator in two ways, which are quite different, and both authentication approaches allow the security administrator to issue the ADMINISTER KEY MANAGEMENT statement. To check if a user is allowed to perform a TDE operation, Oracle Database checks whether the user has the ADMINISTER KEY MANAGEMENT privilege or was authenticated using the SYSKM administrative privilege. Any ADMINISTER KEY MANAGEMENT statement will be allowed for the following users:
- A user who is granted the
SYSKMadministrative privilege (this grant is recorded in the password file) and issues theADMINISTER KEY MANAGEMENTstatement from a session that connected to the database using theAS SYSKMclause. For example:sqlplus c##sec_admin AS SYSKM Enter password: passwordThe reason for this is that
ADMINISTER KEY MANAGEMENTstatements need to be supported when the Oracle data dictionary is not available. The only way to do the necessary privilege check in that situation is to check for theSYSKMadministrative privilege in the password file. Note that the system needs to be configured with a password file in order to be able to grant theSYSKMadministrative privilege to a user. If the user needs to performADMINISTER KEY MANAGEMENToperations such as opening the TDE keystore when the Oracle database is in theMOUNTEDstate, then the user must be granted theSYSKMadministrative privilege. - A user who has been granted the
ADMINISTER KEY MANAGEMENTsystem privilege, and logs in to the database without theAS SYSKMclause. For example:sqlplus c##sec_officer Enter password: password
To configure TDE column or tablespace encryption, you do not need the SYSKM or ADMINISTER KEY MANAGEMENT privileges. You must have the following privileges to encrypt table columns and tablespaces:
-
CREATE TABLE -
ALTER TABLE -
CREATE TABLESPACE -
ALTER TABLESPACE(for online and offline tablespace encryption) -
ALTER DATABASE(for offline tablespace encryption)
Parent topic: Introduction to Transparent Data Encryption
Types and Components of Transparent Data Encryption
Transparent Data Encryption can be applied to individual columns or entire tablespaces.
- About Transparent Data Encryption Types and Components
You can encrypt sensitive data at the column level or the tablespace level. - How Transparent Data Encryption Column Encryption Works
Transparent Data Encryption (TDE) column encryption protects confidential data, such as credit card and Social Security numbers, that is stored in table columns. - How Transparent Data Encryption Tablespace Encryption Works
Transparent Data Encryption (TDE) tablespace encryption enables you to encrypt an entire tablespace. - How the Keystore for the Storage of TDE Master Encryption Keys Works
To control the encryption, you use a keystore and a TDE master encryption key. - Supported Encryption and Integrity Algorithms
The supported Advanced Encryption Standard cipher keys, including tablespace and database encryption keys, can be either 128, 192, or 256 bits long.
Parent topic: Introduction to Transparent Data Encryption
About Transparent Data Encryption Types and Components
You can encrypt sensitive data at the column level or the tablespace level.
At the column level, you can encrypt data using selected table columns. TDE tablespace encryption enables you to encrypt all of the data that is stored in a tablespace.
Both TDE column encryption and TDE tablespace encryption use a two-tiered key-based architecture. Unauthorized users, such as intruders who are attempting security attacks, cannot read the data from storage and back up media unless they have the TDE master encryption key to decrypt it.
Parent topic: Types and Components of Transparent Data Encryption
How Transparent Data Encryption Column Encryption Works
Transparent Data Encryption (TDE) column encryption protects confidential data, such as credit card and Social Security numbers, that is stored in table columns.
TDE column encryption uses the two-tiered key-based architecture to transparently encrypt and decrypt sensitive table columns. The TDE master encryption key is stored in an external security module, which can be an Oracle software keystore or hardware keystore. This TDE master encryption key encrypts and decrypts the TDE table key, which in turn encrypts and decrypts data in the table column.
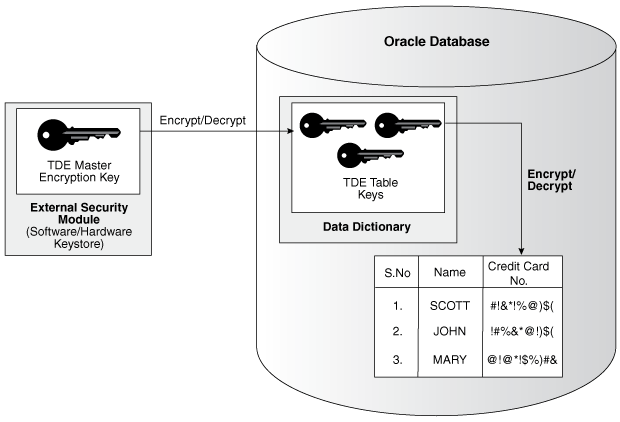
Figure 2-1 shows an overview of the TDE column encryption process.
As shown in Figure 2-1, the TDE master encryption key is stored in an external security module that is outside of the database and accessible only to a user who was granted the appropriate privileges. For this external security module, Oracle Database uses an Oracle software keystore (wallet, in previous releases) or hardware security module (HSM) keystore. Storing the TDE master encryption key in this way prevents its unauthorized use.
Using an external security module separates ordinary program functions from encryption operations, making it possible to assign separate, distinct duties to database administrators and security administrators. Security is enhanced because the keystore password can be unknown to the database administrator, requiring the security administrator to provide the password.
When a table contains encrypted columns, TDE uses a single TDE table key regardless of the number of encrypted columns. Each TDE table key is individually encrypted with the TDE master encryption key. All of the TDE table keys are located together in the colklc column of the ENC$ data dictionary table. No keys are stored in plaintext (message text that has not been encrypted).
Parent topic: Types and Components of Transparent Data Encryption
How Transparent Data Encryption Tablespace Encryption Works
Transparent Data Encryption (TDE) tablespace encryption enables you to encrypt an entire tablespace.
All of the objects that are created in the encrypted tablespace are automatically encrypted. TDE tablespace encryption is useful if your tables contain sensitive data in multiple columns, or if you want to protect the entire table and not just individual columns. You do not need to perform a granular analysis of each table column to determine the columns that need encryption.
In addition, TDE tablespace encryption takes advantage of bulk encryption and caching to provide enhanced performance. The actual performance impact on applications can vary.
TDE tablespace encryption encrypts all of the data stored in an encrypted tablespace including its redo data. TDE tablespace encryption does not encrypt data that is stored outside of the tablespace. For example, BFILE data is not encrypted because it is stored outside the database. If you create a table with a BFILE column in an encrypted tablespace, then this particular column will not be encrypted.
All of the data in an encrypted tablespace is stored in encrypted format on the disk. Data is transparently decrypted for an authorized user having the necessary privileges to view or modify the data. A database user or application does not need to know if the data in a particular table is encrypted on the disk. In the event that the data files on a disk or backup media is stolen, the data is not compromised.
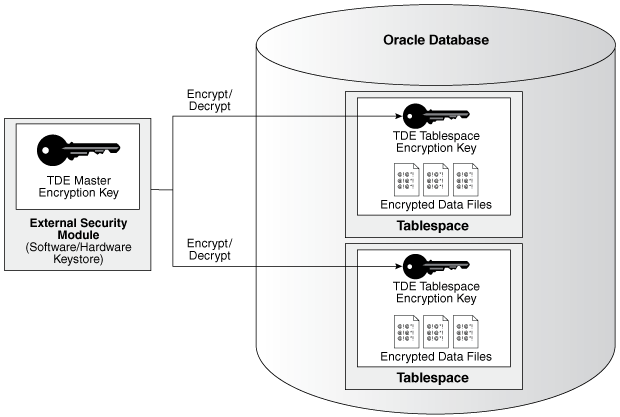
TDE tablespace encryption uses the two-tiered, key-based architecture to transparently encrypt (and decrypt) tablespaces. The TDE master encryption key is stored in an external security module (software or external keystore). This TDE master encryption key is used to encrypt the TDE tablespace encryption key, which in turn is used to encrypt and decrypt data in the tablespace.
Figure 2-2 shows an overview of the TDE tablespace encryption process.
Note:
The encrypted data is protected during operations such as JOIN and SORT. This means that the data is safe when it is moved to temporary tablespaces. Data in undo and redo logs is also protected.
TDE tablespace encryption also allows index range scans on data in encrypted tablespaces. This is not possible with TDE column encryption.
Oracle Database implements the following features to TDE tablespace encryption:
-
It uses a unified TDE master encryption key for both TDE column encryption and TDE tablespace encryption.
-
You can reset the unified TDE master encryption key. This provides enhanced security and helps meet security and compliance requirements.
Parent topic: Types and Components of Transparent Data Encryption
How the Keystore for the Storage of TDE Master Encryption Keys Works
To control the encryption, you use a keystore and a TDE master encryption key.
- About the Keystore Storage of TDE Master Encryption Keys
Oracle Database provides a key management framework for Transparent Data Encryption that stores and manages keys and credentials. - Benefits of the Keystore Storage Framework
The key management framework provides several benefits for Transparent Data Encryption. - Types of Keystores
Oracle Database supports software keystores, Oracle Key Vault, and other PKCS#11 compatible key management devices.
Parent topic: Types and Components of Transparent Data Encryption
About the Keystore Storage of TDE Master Encryption Keys
Oracle Database provides a key management framework for Transparent Data Encryption that stores and manages keys and credentials.
The key management framework includes the keystore to securely store the TDE master encryption keys and the management framework to securely and efficiently manage keystore and key operations for various database components.
The Oracle keystore stores a history of retired TDE master encryption keys, which enables you to change them and still be able to decrypt data that was encrypted under an earlier TDE master encryption key.
Benefits of the Keystore Storage Framework
The key management framework provides several benefits for Transparent Data Encryption.
-
Enables separation of duty between the database administrator and the security administrator who manages the keys. You can grant the
ADMINISTER KEY MANAGEMENTorSYSKMprivilege to users who are responsible for managing the keystore and key operations. -
Facilitates compliance, because it helps you to track encryption keys and implement requirements such as keystore password rotation and TDE master encryption key reset or rekey operations.
-
Facilitates and helps enforce keystore backup requirements. A backup is a copy of the password-protected software keystore that is created for all of the critical keystore operations.
You must make a backup of the keystore for all of the critical keystore operations. You must also make a backup of the TDE master encryption key before you reset or rekey this TDE master encryption key.
-
Enables the keystore to be stored on an ASM file system. This is particularly useful for Oracle Real Application Clusters (Oracle RAC) environments where database instances share a unified file system view.
-
Enables reverse migration from an external keystore to a file system-based software keystore. This option is useful if you must migrate back to a software keystore.
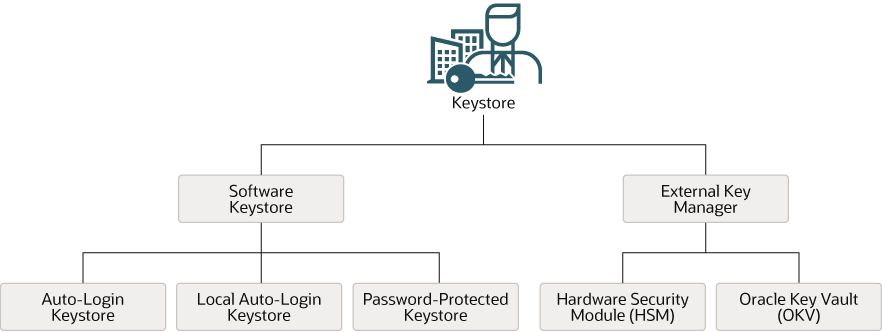
Types of Keystores
Oracle Database supports software keystores, Oracle Key Vault, and other PKCS#11 compatible key management devices.
Figure 2-3 Oracle Database Supported Keystores
Description of "Figure 2-3 Oracle Database Supported Keystores"
These keystores are as follows:
-
Auto-login software keystores: Auto-login software keystores are protected by a system-generated password, and do not need to be explicitly opened by a security administrator. Auto-login software keystores are automatically opened when accessed. Auto-login software keystores can be used across different systems. If your environment does not require the extra security provided by a keystore that must be explicitly opened for use, then you can use an auto-login software keystore. Auto-login software keystores are ideal for unattended scenarios (for example, Oracle Data Guard standby databases).
-
Local auto-login software keystores: Local auto-login software keystores are auto-login software keystores that are local to the computer on which they are created. Local auto-login keystores cannot be opened on any computer other than the one on which they are created. This type of keystore is typically used for scenarios where additional security is required (that is, to limit the use of the auto-login for that computer) while supporting an unattended operation. You cannot use local auto-open wallets in Oracle RAC-enabled databases, because only shared wallets (in ACFS or ASM) are supported.
-
Password-protected software keystores: Password-protected software keystores are protected by using a password that you create. You must open this type of keystore before the keys can be retrieved or used.
Software keystores can be stored in Oracle Automatic Storage Management (Oracle ASM), Oracle Automatic Storage Management Cluster File System (Oracle ACFS), or regular file systems.
Under External Keystore Manager are the following categories:
-
Oracle Key Vault (OKV): Oracle Key Vault is a software appliance that provides continuous key availability and scalable key management through clustering with up to 16 Oracle Key Vault nodes, potentially deployed across geographically distributed data centers. It is purpose-build for Oracle Database and its many deployment models (Oracle RAC, Oracle Data Guard, Exadata, multitenant environments). In addition, Oracle Key Vault provides online key management for Oracle GoldenGate encrypted trail files and encrypted ACFS. It is also certified for ExaCC and Autonomous Database (dedicated) (ADB-D on ExaCC). Oracle Key Vault is also available in the OCI Marketplace and can be deployed in your OCI tenancy quickly and easily.
-
Hardware Security Module (HSM): Hardware security modules are third-party physical devices that provide secure storage for encryption keys, in external keystores. HSMs also provide secure computational space (memory) to perform encryption and decryption operations. If you are using an HSM, data encryption keys must decrypted by the TDE master encryption key inside the FIPS-boundary of the HSM. This means that the TDE master encryption key never leaves the internal FIPS boundary of the HSM, which explains the high (network) load when a database with high transactional load (for example, Exadata with hundreds of encrypted PDBs) continues to send data encryption keys to the HSM.
Related Topics
Supported Encryption and Integrity Algorithms
The supported Advanced Encryption Standard cipher keys, including tablespace and database encryption keys, can be either 128, 192, or 256 bits long.
Tablespace and database encryption use AES128 by default, unless the default encryption algorithm is changed to AES192 or AES256 with the TABLESPACE_ENCRYPTION_DEFAULT_ALGORITHM dynamic initialization parameter.
For TDE column encryption, salt is added by default to plaintext before encryption unless specified otherwise. You cannot add salt to indexed columns that you want to encrypt. For indexed columns, choose the NO SALT parameter for the SQL ENCRYPT clause.
For TDE tablespace encryption and database encryption, the default encryption algorithm is AES128. The default encryption algorithm for TDE column encryption is AES192.
You can change encryption algorithms and encryption keys on existing encrypted columns by setting a different algorithm with the SQL ENCRYPT clause.
Table 2-1 lists the supported encryption algorithms.
Table 2-1 Supported Encryption Algorithms for Transparent Data Encryption
| Algorithm | Key Size | Parameter Name |
|---|---|---|
|
Advanced Encryption Standard (AES) |
|
|
|
|
|
|
|
|
256 bits |
|
|
|
128 bits |
|
|
Triple Encryption Standard (DES) |
168 bits |
|
For integrity protection of TDE column encryption, the SHA-1 hashing algorithm is used. (Starting with Oracle Database release 21c, SHA-1 is deprecated. If you use TDE column encryption, then Oracle recommends that you implement TDE tablespace encryption instead.)
Related Topics
Parent topic: Types and Components of Transparent Data Encryption
Transparent Data Encryption in a Multitenant Environment
In a multitenant environment, you can configure keystores for either the entire container database (CDB) or for individual pluggable databases (PDBs).
Oracle Database supports the following multitenant modes for the management of keystores:
-
United mode enables you to configure one keystore for the CDB root and any associated united mode PDBs. United mode operates much the same as how TDE was managed in an multitenant environment in previous releases.
-
Isolated mode enables you to create and manage both keystores and TDE master encryption keys in an individual PDB. Different isolated mode PDBs can have different keystore types.
You can use these modes to configure software keystores, external keystores, and Oracle Key Vault keystores.
Depending on your site’s needs, you can use a mixture of both united mode and isolated mode. For example, if you want most of the PDBs to use one type of a keystore, then you can configure the keystore type in the CDB root (united mode). For the PDBs in this CDB that must use a different type of keystore, then you can configure the PDB itself to use the keystore it needs (isolated mode). The isolated mode setting for the PDB will override the united mode setting for the CDB.
Before you can configure keystores for use in united or isolated mode, you must perform a one-time configuration by using initialization parameters. To configure keystores for united mode and isolated mode, you use the ADMINISTER KEY MANAGEMENT statement. After you restart the database, where you can use the ADMINISTER KEY MANAGEMENT statement commands will change. For example, before the configuration, you could not use the EXTERNAL STORE clause in the ADMINISTER KEY MANAGEMENT statement in the CDB root, but after the configuration, you can.
How Configuring Transparent Data Encryption Works
To configure Transparent Data Encryption, you must perform a one-time setup before you create keystores and encrypt data.
Before you can configure keystores and begin to encrypt data, you must perform a one-time configuration using the WALLET_ROOT and TDE_CONFIGURATION parameters to designate the location and type of keystores that you plan to create.
The WALLET_ROOT parameter specifies the keystore directory location. Before you set WALLET_ROOT, ensure that you have an existing directory that you can use to store keystores. (Typically, this directory is called wallet.)
The TDE_CONFIGURATION parameter specifies the type of keystore (software keystore, external keystore, or Oracle Key Vault keystore). If you omit the TDE_CONFIGURATION parameter, then Oracle Database uses the sqlnet.ora file settings. After you set the type of keystore using TDE_CONFIGURATION, when you create the keystore, Oracle Database creates a directory within the WALLET_ROOT location for the keystore type. For example, if you set TDE_CONFIGURATION to FILE, for Transparent Data Encryption keystores, then Oracle Database creates a directory named tde (lower case) within the wallet directory. If you want to migrate from one keystore type to another, then you must first set TDE_CONFIGURATION parameter to the keystore type that you want to use, and then use the ADMINISTER KEY MANAGEMENT statement to perform the migration. For example, you can migrate from a hardware security module (HSM) keystore to a TDE keystore.
The KEYSTORE_MODE column of the V$ENCRYPTION_WALLET dynamic view shows whether united mode or isolated mode has been configured.
Note:
In previous releases, theSQLNET.ENCRYPTION_WALLET_LOCATION parameter was used to define the keystore directory location. This parameter has been deprecated. Oracle recommends that you use the WALLET_ROOT static initialization parameter and TDE_CONFIGURATION dynamic initialization parameter instead.
Related Topics
Parent topic: Introduction to Transparent Data Encryption
Transparent Data Encryption Keystore Search Order
The search order for the TDE keystore depends on how you have set either the instance initialization parameters, the sqlnet.ora parameters, or the environment variables.
Oracle Database retrieves the keystore by searching in these locations, in the following order:
-
The location set by the
WALLET_ROOTinstance initialization parameter, when theKEYSTORE_CONFIGURATIONattribute of theTDE_CONFIGURATIONinitialization parameter is set. Oracle recommends that you use this parameter to configure the keystore location. -
If the
KEYSTORE_CONFIGURATIONattribute of theTDE_CONFIGURATIONinitialization parameter is not set orWALLET_ROOTis not set, then the location specified by theENCRYPTION_WALLET_LOCATIONsetting (now deprecated in favor ofWALLET_ROOT) in thesqlnet.orafile. -
If none of these parameters are set, and if the
ORACLE_BASEenvironment variable is set, then the$ORACLE_BASE/admin/db_unique_name/walletdirectory. IfORACLE_BASEis not set, then$ORACLE_HOME/admin/db_unique_name/wallet.
Parent topic: Introduction to Transparent Data Encryption